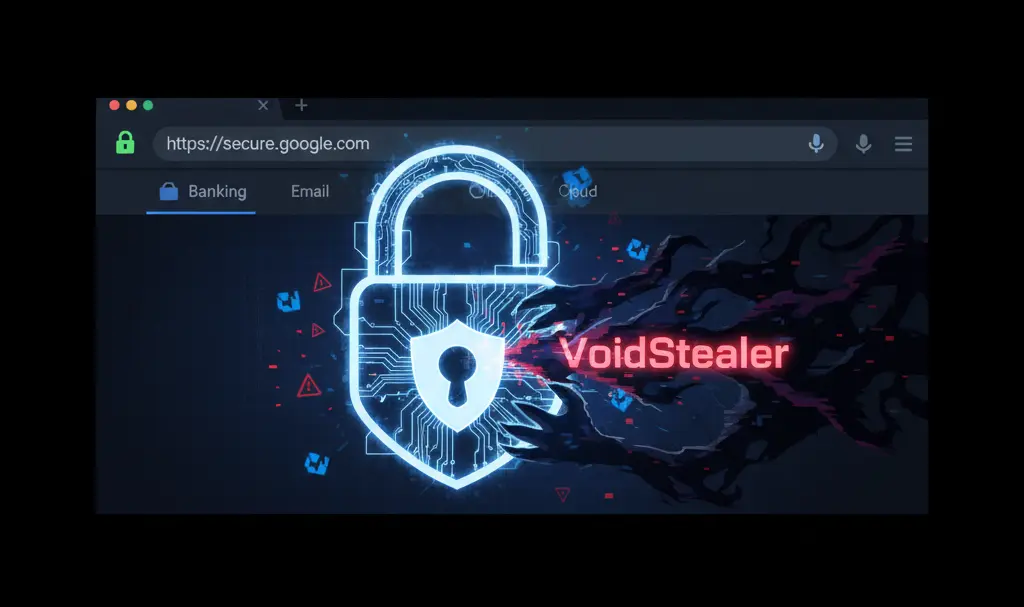
Safeguarding Your Passwords: Protecting Google Chrome from VoidStealer
Google Chrome’s built-in password manager is a highly convenient tool, designed to automatically generate strong passwords and securely fill them into web forms. However, this convenience is now being targeted by advanced cyber threats. This article explains how sophisticated malware like VoidStealer attempts to exploit the password manager and provides crucial advice on how to defend yourself against such attacks.
How VoidStealer Attacks Google Chrome
VoidStealer is a newly identified malware that leverages a vulnerability related to Google Chrome’s Application-Bound Encryption (ABE) feature. ABE, introduced in Chrome around June 2024, was designed to enhance password security by encrypting stored credentials in a way that prevents simple file copying from granting unauthorized access. Previously, an attacker could potentially copy Chrome’s application files from a user’s profile and decrypt passwords offline. ABE aims to tie these encrypted passwords to the specific Chrome installation, making such direct theft much harder.
However, experts from Gen Digital, the parent company of antivirus brands like AVG, Avira, and Avast, report that VoidStealer is the first malware observed to exploit a newly discovered weakness in this system. For Chrome to access and decrypt passwords from its manager, the browser temporarily loads a file called `v20_master_key` into its memory. This master key is essential for decrypting all stored user passwords.
VoidStealer operates by silently running in the background, invisible to the user. It patiently waits for the precise moment when Chrome initializes, typically during browser startup. During this startup process, when the `v20_master_key` is briefly present in the temporary memory to decrypt user passwords, the malware intercepts and steals this critical key.
To ensure it doesn’t miss this fleeting opportunity, VoidStealer embeds itself within dynamic-link library (DLL) files. DLLs are shared code libraries used by many programs, including web browsers. By infecting these DLLs, the malware can vigilantly monitor every time Chrome launches, positioning itself to intercept the master key as soon as it appears in memory. This advanced method means that even if ABE protects the stored files, the in-memory key can still be compromised.
How to Protect Yourself from Password Theft by Hackers
The existence of VoidStealer does not mean that using Google Chrome’s password manager is inherently unsafe. Instead, it underscores the importance of practicing good cybersecurity hygiene. By following a few straightforward steps, you can significantly enhance your protection:
* **Utilize Strong, Unique Passwords:** Always use the password generator feature to create complex, unique passwords for every online account. Reusing passwords across multiple services is a major security risk, as a breach on one site can compromise all your accounts.
* **Enable Two-Factor Authentication (2FA):** Implement 2FA wherever possible. Ideally, use an authenticator app like Google Authenticator, which generates time-sensitive codes. This adds a crucial layer of security, requiring a second verification step even if your password is stolen.
* **Keep Google Chrome Updated:** Regularly update your Google Chrome browser on both your smartphone and computer. Updates often include critical security patches that fix vulnerabilities exploited by malware like VoidStealer. On Android devices, updates are done through the Google Play Store. On desktop computers, you can usually find this option via the browser menu: Help → About Google Chrome.
* **Be Cautious with Downloads:** Never download files from unverified or untrustworthy sources. Malicious software is often disguised as legitimate programs or documents. Always verify the source before downloading anything to prevent malware from infecting your system.
* **Avoid Suspicious Links:** Exercise extreme caution before clicking on links in emails, text messages, or instant messages, especially if they are unexpected or from unknown senders. These are common tactics used in phishing attacks to trick you into revealing sensitive information or downloading malware.
While technology provides many safeguards, nothing replaces sound judgment. These five simple steps, combined with a healthy dose of skepticism online, will significantly enhance your digital safety and help protect you from sophisticated threats.
Frequently Asked Questions (FAQ)
What exactly is Application-Bound Encryption (ABE) and how does VoidStealer bypass it?
Application-Bound Encryption (ABE) is a security feature introduced in Google Chrome to tie encrypted passwords to a specific browser installation. This makes it harder for attackers to steal password files and decrypt them on a different system. VoidStealer bypasses ABE not by cracking the encryption on stored files, but by intercepting the `v20_master_key` when it is temporarily loaded into Chrome’s memory during the browser’s startup. By embedding itself in DLL files, the malware monitors Chrome’s launch and captures this key before it can be fully secured.
Can I still use Google Chrome’s built-in password manager safely after reading about VoidStealer?
Yes, you can still use Google Chrome’s password manager safely, but it’s crucial to implement additional security measures. VoidStealer highlights the need for a multi-layered defense. By combining the password manager’s convenience with strong, unique passwords, two-factor authentication, regular browser updates, and vigilance against suspicious downloads and links, you significantly reduce your risk. The password manager remains a valuable tool when used responsibly with these precautions.
Besides the steps mentioned, are there any other advanced precautions I should take to protect my passwords?
Beyond the essential steps, consider using a dedicated hardware security key (like a YubiKey) for 2FA on critical accounts, as these offer even stronger protection against phishing than authenticator apps. Regularly back up your important data, enable a reputable antivirus/anti-malware solution, and periodically review your security settings on all online accounts. Also, be aware of the “principle of least privilege” for software, only granting necessary permissions.
How can I identify if my system might be infected with malware like VoidStealer?
Detecting sophisticated malware like VoidStealer can be challenging as it often operates stealthily. However, potential signs of infection can include unexplained system slowdowns, unusual network activity, unexpected browser behavior (e.g., new toolbars, redirects), frequent crashes, or a noticeable increase in disk activity when your browser is closed. The best defense is proactive: use up-to-date antivirus software, keep your operating system and all applications patched, and monitor your accounts for any unauthorized activity.
Source: Gen Digital. Opening photo: Gemini